“Boss, I left my cell in the bar last night…”
[vc_row][vc_column][vc_hoverbox image=”2661″ primary_title=”” hover_title=”“Boss, I left my cell in the…
Have you ever Googled “Cyber Crime”?
[vc_row][vc_column][vc_hoverbox image=”2656″ primary_title=”” hover_title=”Have you ever Googled “Cyber Crime?“”][/vc_hoverbox][/vc_column][/vc_row][vc_row][vc_column][vc_column_text css_animation=”none”]The…
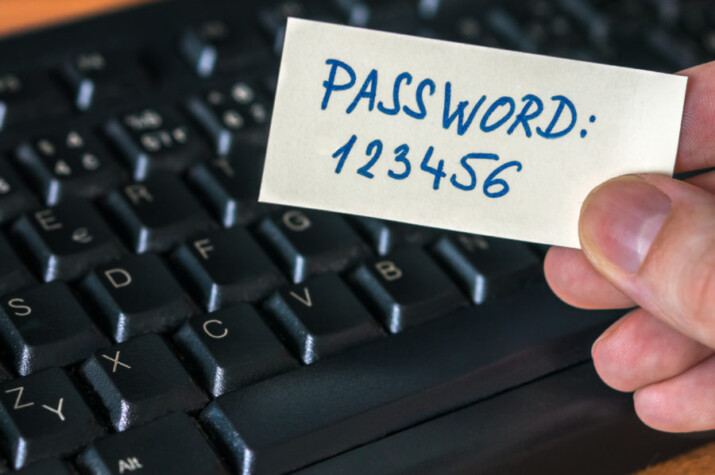
3 in 4 staff would fail a simple password check
[vc_row][vc_column width=”1/2″][vc_column_text]You want your staff to watch this video. Because…
Think your password is secure? Think again
A password policy designed for federal agencies must be secure,…
Not all hackers are cybercriminals
Newspaper headlines and Hollywood movies have shaped our understanding of…
The lowdown on cloud security
If you’re thinking of transitioning your business to the cloud,…
Is your IT security proactive?
Do you spend hours obsessing about the inner workings of…
Secure your Mac computer in 6 easy ways
If you’re a Mac user, data privacy and security should…
4 types of hackers that may target SMBs
When it comes to cyberattacks, most business owners get hung…
Don’t let hackers fool you with these tricks
The volume of malicious cyber attacks is increasing every year.…