Support your growth with proactive IT solutions
Bounce back from issues with fast tech support
Work with a stellar IT team that cares
Feeling Lost in Space
With Your IT?
- Are you constantly battling outages or struggling with slow response times?
- Do you need managed IT services that go beyond quick fixes?
- Does your current provider leave you feeling unsupported when you need them most?
If your IT systems aren’t well-oiled, up-to-date and running smoothly, BrightCare managed services can help.
Don’t Fly Solo
With technology moving at the speed of light, you need sophisticated technical expertise to keep up. When you choose BrightFlow, you get a partner, not just another vendor. We listen carefully and get to know you. Because the more we know about your business and where it’s going, the better we’re able to help you get there.
Essentially, we become an extension of your team. Not outsiders who fix things and then leave you on your own until the next issue arises.
- No forced long-term contracts
- 100% CSAT score
- In business since 2013
The Care Your Organization Deserves
Our managed service is called BrightCare because we care deeply: Not just about your technology, but for you and your employees, too. We only hire technical minds who love to help people first. People who have compassion for what you’re going through.
Avoiding the Downside
Without reliable IT support, you could be overpaying for on-site IT staff or stuck dealing with expensive and frustrating downtime.
When your systems and operations run fast and efficiently, you’ll save time and money in the long run.
Looking for the Perfect Partner?
Finding smart, experienced tech professionals you can’t wait to work with can be tough. Our IT Services Buyer’s Guide helps make the search easy and maybe even fun.
In this free guide, you’ll discover:

- Why you need an IT strategy.
- How to protect the most important thing in your business.
- Why you should be highly skeptical of all IT support companies.
- What every IT support company wishes you knew about IT.
- And much more.
People Talk.
It takes a good leader to make a great team, and that’s what we get with BrightFlow. Thanks, Brian, for leading your team well!
BrightFlow is very hands-on and supporting, with great turn-around times. I highly recommend them!
If you want a knowledgeable team with great customer service, give BrightFlow a try.
Thanks for all you do, Brian!
Conquer IT


Managed IT Services FAQs
What are managed IT services?
With managed IT services, an organization outsources its IT support responsibilities to a third-party provider (a managed service provider or MSP). Instead of handling IT tasks and duties internally, businesses partner with an MSP to manage their IT systems and infrastructure for a recurring fee.
An outsourced MSP can offer a wide range of services, such as:
- Cybersecurity solutions: Includes implementation and management of security measures like firewalls, antivirus software, intrusion detection systems and security awareness training to protect against cyber threats.
- Data backup and disaster recovery: Regular backups of critical data and robust disaster recovery plans minimize downtime and data loss in case of emergencies and are typically included in managed IT services.
- Support: Provides users with expert assistance in addressing technical issues.
- Network monitoring and management: Offers proactive monitoring of network infrastructure to identify and resolve potential problems before they impact users.
- Cloud computing services: Includes assistance with cloud migration, management of cloud infrastructure and optimization of cloud resources.
What are the benefits of managed IT services?
When you partner with an MSP you benefit from:
- Access to a team with deep expertise: Tap into the know-how of an experienced team of IT professionals with diverse skills.
- Reduced costs: Avoid hiring and retaining in-house IT staff, reduce downtime and manage technology investments with IT support services.
- Increased efficiency: Let the IT experts handle your technology needs while you focus on your core business functions.
- Enhanced security: Protect critical data while strengthening your defenses against cyberattacks with advanced security measures.
- Improved productivity: With smoother IT operations, you can minimize disruptions and provide employees with reliable technology.
What types of businesses benefit most from managed IT services?
Managed IT services can benefit many businesses, but they’re especially helpful for certain organizations. Small to medium-sized businesses (SMBs) that don’t have the budget or need for a full-time IT department can get all the support they need without the expense of hiring an entire team.
Businesses that handle sensitive data, like those in the healthcare or finance sectors, also benefit from managed services because of the strict compliance regulations and robust security protocols. Managed IT services are a great option for any company that needs 24/7 support or wants to be proactive with their IT approach.
What is the difference between break-fix IT support and managed IT services?
The main difference between these two approaches is how they handle IT issues. Break-fix is a reactive model where you call an IT professional only when something is already broken. Managed IT services, on the other hand, are proactive. A managed service provider (MSP) continuously monitors your systems to prevent problems before they can even happen. This approach helps minimize downtime, improve system stability and reduce overall IT costs in the long run.
What should I look for when choosing an MSP?
Every MSP is different. Choosing the right one is important for your business success. Consider these factors:
- Experience and expertise: Look for a provider with a strong track record and expertise in your specific industry.
- Service level agreements (SLAs): A good MSP will have clearly defined SLAs that outline response times, service availability, and performance guarantees.
- Security practices: Make sure the MSP has robust security measures in place to protect your sensitive data.
- Communication: Choose a provider that communicates effectively and provides regular reports on the health of your IT systems.
- References and reviews: Check client testimonials and online reviews to get a feel for their reputation and customer satisfaction.
Can managed IT services packages be customized?
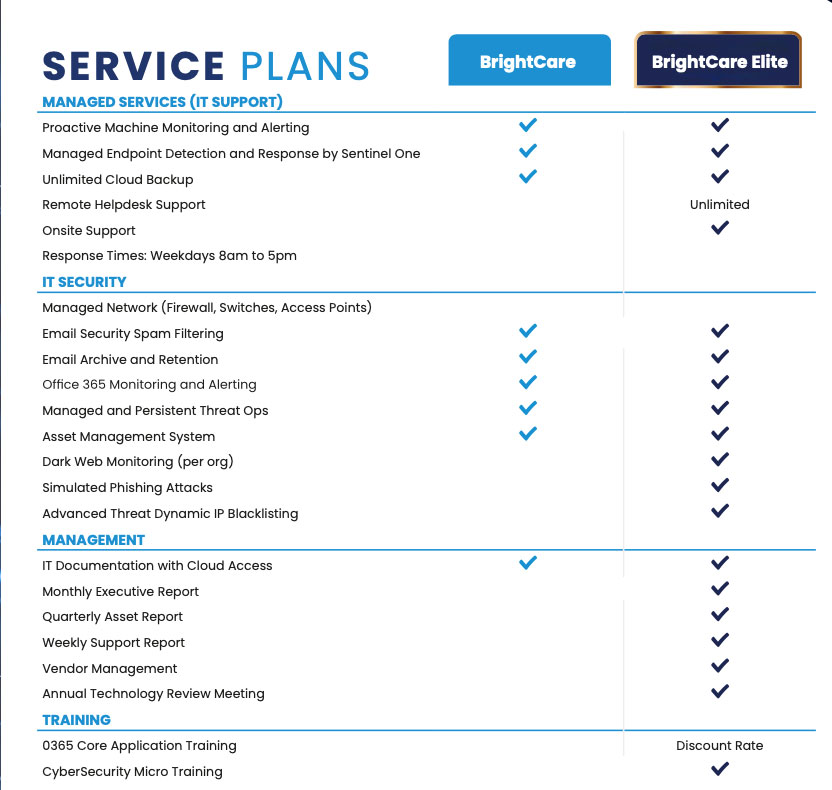
Most MSPs offer flexible service packages that can be tailored to specific needs and budget. Choose the services that are most important currently and adjust the package as your needs evolve.
How do I get started with managed IT services?
Reach out to potential MSP partners to discuss your organization’s goals and IT needs. Expect them to assess your current IT infrastructure and respond with a proposal outlining the recommended services and costs.